The conventional notion of a workplace is progressively transitioning into remote work in the present digital age. Many people are now able to work from the convenience of their homes because of technological improvements. Nevertheless, despite the appearance of simplicity, working remotely has its share of difficulties, particularly when it comes to ensuring secure communication.
The cloud, other collaborative technologies, and increasingly potent broadband access can help remote enterprises prosper. However, this model may potentially raise the risk of a cyberattack. Employees can be utilizing unfamiliar software, working in novel ways, and using services with less secure technology. Cybercriminals are aware of this, and they are also aware that as more individuals go online, there are more opportunities to exploit security flaws and user mistakes to access private or protected data.
Why is Secure Communication Essential?
Consider a scenario where you share sensitive project details via email with a coworker, only to discover later that it was compromised by a cyber attacker. This breach not only risks the project but also damages your firm’s credibility and standing. As the distinction between the workspace and home blur, it’s imperative to ensure that your communication lines are just as secure as they would be in a traditional brick-and-mortar office setting.
Start with Basic Security Measures
It’s wise to go through the fundamentals before diving into more complicated tactics. Here are a few simple but efficient ways to protect your communications:
Strong Passwords
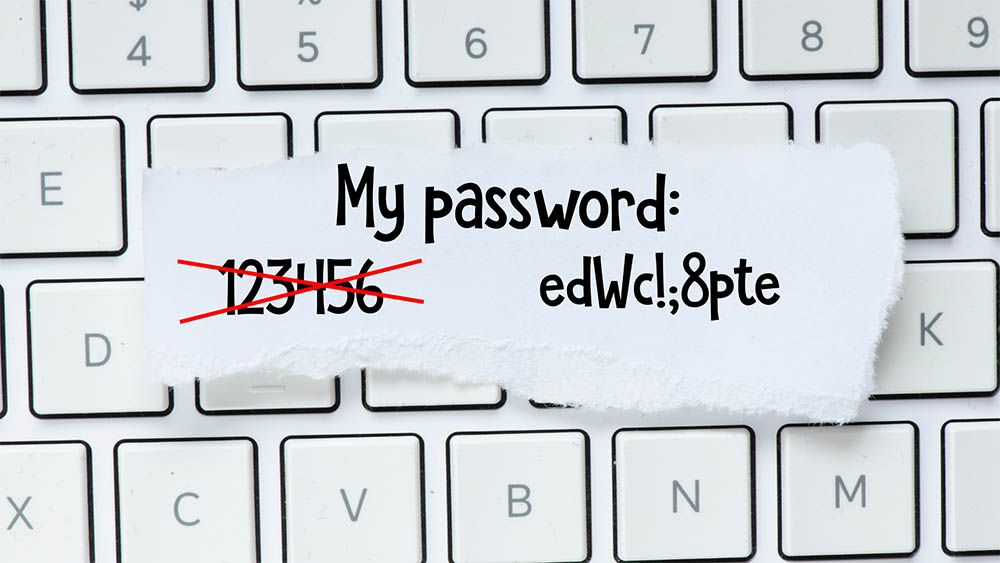 The importance of robust, unique passwords as a primary security tool cannot be overstated. However, people typically overlook this fundamental measure. Even though it might seem appealing to use easy-to-remember or recycled passwords across different platforms, it significantly weakens your security.
The importance of robust, unique passwords as a primary security tool cannot be overstated. However, people typically overlook this fundamental measure. Even though it might seem appealing to use easy-to-remember or recycled passwords across different platforms, it significantly weakens your security.
An effective password typically includes, at minimum, 12 characters comprising upper and lower-case letters, numbers, and special symbols. Using meaningful phrases or sentences while keeping them cryptic for others can enhance security and ease of memory.
If the task of creating and remembering complex passwords for multiple accounts seems too taxing, consider employing a reliable password manager. All of your credentials can be safely stored by these systems.
Two-factor authentication (2FA)
Enabling two-factor authentication, if possible, adds an extra degree of protection by requiring a second form of verification in addition to a password.
To enable 2FA, typically go to your account settings and follow the service’s setup instructions. It’s a tiny irritation that pays dividends in terms of security, ensuring that even if your password is compromised, your communication accounts remain secure.
Secure Wi-Fi
Ascertain that your home Wi-Fi network is password-protected and using WPA3 security. Because of its vulnerability to cyber-attacks, public Wi-Fi should be avoided wherever feasible.
Keep Software Updated
Make it a habit to keep all of your software up to date, including your communication tools. For starters, they address known security flaws that hackers can use to obtain unauthorized access to your systems or intercept your communications.
By updating your operating system, software, and communication tools regularly, you ensure that these vulnerabilities are patched, reducing the danger of intrusions dramatically. Additionally, software upgrades usually include performance increases, bug repairs, and new features that improve the overall functionality and dependability of your communication tools.
Making it a practice to stay current with software upgrades is therefore not only an issue of security but also a way to ensure that your communication operations work smoothly and efficiently.
Virtual Private Network (VPN)
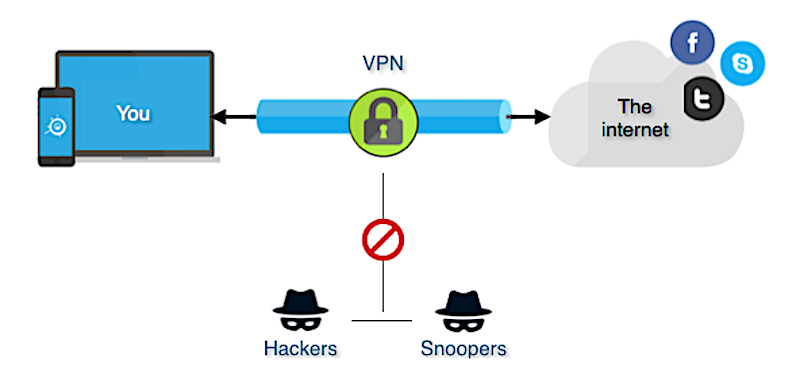 When conversing, using a VPN can add an extra degree of security by encrypting your internet connection. A VPN, in essence, establishes a safe and encrypted connection between your device and a remote server.
When conversing, using a VPN can add an extra degree of security by encrypting your internet connection. A VPN, in essence, establishes a safe and encrypted connection between your device and a remote server.
When you use a VPN to access the internet, all of your web traffic is sent through an encrypted tunnel, making it exceedingly impossible for hackers, ISPs, or eavesdroppers to intercept or decipher your data. A VPN not only protects your data but also covers your IP address, maintaining your online anonymity.
Training and Policies
Employees are frequently the weakest link in the security chain of a corporation. Training them on best practices can go a long way toward guaranteeing secure connections.
Use the Cloud
More and more businesses are choosing to keep their data in the cloud and rely on cloud computing to manage their business processes in a world where cyberattacks are front-page news in the major media. Nothing could be further from the truth when it comes to the security of data and computer systems and this shift to the cloud. Since cybersecurity was a top priority when designing its infrastructure, the Cloud is secure for files and programs.
Written Policies
Have a documented policy describing the dos and don’ts of internal communication. Make it easily accessible and known to all team members.
Monitoring and Audits
While it may sound a little Orwellian, monitoring communications is often important to guarantee that all rules are followed. Regular audits might assist in identifying any flaws in your security system. Conduct security audits regularly to detect weaknesses. This could include everything from checking firewall settings to examining how data is moved throughout your firm.
Incident Reporting
Encourage staff to report any questionable conduct quickly. A security compromise can often be mitigated by quick action.
Final Thoughts
The trend toward remote employment is likely to continue, as are the difficulties connected with maintaining secure connections. You may considerably reduce risks by using a multi-layered approach that combines fundamental security procedures, specialist tools, training, and monitoring. Remember that the key to secure communication is technology and cultivating a security-aware culture within your firm.

