Introduction
Smart contracts have revolutionized the way we perceive digital agreements in the blockchain ecosystem. As self-executing contracts with the terms of the agreement directly written into code, they offer a level of efficiency and trustworthiness that traditional contracts can’t match. However, with great innovation comes significant responsibility, especially in understanding and mitigating the risks associated with these digital contracts. This guide delves into the vulnerabilities of smart contracts, offering insights for developers, investors, and enthusiasts alike.
Fundamentals of Smart Contracts
What are Smart Contracts?
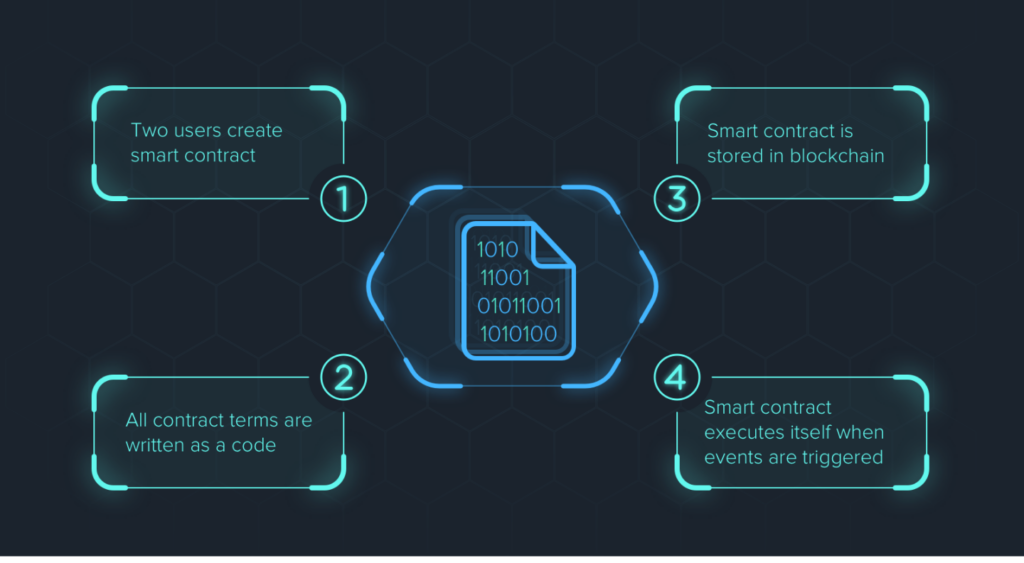
Smart contracts are automated agreements executed on blockchain platforms. They are programmed to automatically enforce and execute the terms of a contract when predetermined conditions are met. This technology is pivotal in various sectors, including finance, real estate, and supply chain management, due to its ability to reduce the need for intermediaries, thereby saving time and costs.
Working Mechanism and Use Cases
The working mechanism of a smart contract involves deploying a set of predefined rules onto the blockchain. Once these rules are triggered by certain actions or conditions, the smart contract executes the agreed-upon terms. Use cases range from automating payments in cryptocurrency transactions to managing agreements in decentralized finance (DeFi) platforms.
Types of Vulnerabilities in Smart Contracts
Coding Errors and Bugs
One of the primary risks in smart contracts arises from coding errors and bugs. Given that smart contracts are immutable once deployed on the blockchain, any flaw in the code can lead to significant vulnerabilities, including financial losses.
Security Flaws and Loopholes
Security flaws, such as reentrancy attacks or overflow/underflow bugs, pose serious threats to smart contracts. These vulnerabilities can be exploited by attackers, leading to unauthorized access or manipulation of contract functions.
External Dependencies and Oracle Risks
Smart contracts often rely on external data sources, known as oracles, to execute certain conditions. However, reliance on these external sources can introduce risks, especially if the oracle data is manipulated or inaccurate.
Notable Smart Contract Failures

Case Studies of Breaches
Several high-profile smart contract failures have highlighted the importance of robust security measures. For instance, the DAO attack in 2016 resulted in the loss of millions of dollars due to a reentrancy vulnerability. These case studies serve as crucial learning points for developers and stakeholders in the blockchain community.
Another notable case is the Parity Multisig Wallet vulnerability in 2017, where a coding error in the smart contract led to the freezing of over $300 million worth of Ether. This incident underscored the critical need for rigorous testing and auditing processes to identify and rectify potential vulnerabilities before deployment.
Analysis of Causes and Consequences
In analyzing these failures, common causes include overlooked security vulnerabilities, inadequate testing, and a lack of understanding of blockchain complexities. The consequences often extend beyond financial losses, affecting trust in the technology and leading to regulatory scrutiny.
Mitigating Risks and Enhancing Security
Best Practices in Smart Contract Development
To mitigate the risks associated with smart contracts, developers must adhere to a set of best practices. This includes thorough testing and debugging, following coding standards, and keeping the contract as simple as possible to avoid unnecessary complexities. Regular updates and patches are also crucial in addressing any newly discovered vulnerabilities.
Tools and Methods for Auditing and Testing
Smart contract auditing is a critical step in ensuring the security and integrity of these digital agreements. Utilizing tools and methods like static analysis, formal verification, and manual code review can significantly reduce the risk of vulnerabilities. Understanding the smart contract auditing cost is vital for developers and companies to allocate appropriate resources for this crucial process.
The Role of Ongoing Monitoring and Updates
Continuous monitoring of smart contracts post-deployment is essential. This involves keeping an eye on transaction patterns and potential security threats. Regular updates based on evolving smart contract security standards and practices are also necessary to maintain the contract’s integrity over time.
The Future of Smart Contract Security
Emerging Trends and Technologies
The future of smart contract security looks promising with the advent of new technologies and methodologies. Innovations like AI-driven security audits and the integration of machine learning algorithms are set to enhance the ability to predict and prevent vulnerabilities in smart contracts.
The Role of AI and Machine Learning
AI and machine learning offer new horizons in smart contract security by providing advanced predictive analytics and automated anomaly detection. These technologies can help in identifying potential risks and vulnerabilities that might be missed during manual audits.
Conclusion
Understanding and mitigating the risks associated with smart contracts is crucial in the blockchain ecosystem. As we have explored, from the fundamentals of smart contracts to the emerging trends in their security, it is clear that continuous learning, adaptation, and investment in security practices are key. For companies and developers, being aware of the smart contract auditing price and engaging with reputable smart contract auditing companies are essential steps in ensuring the success and reliability of their blockchain ventures.

